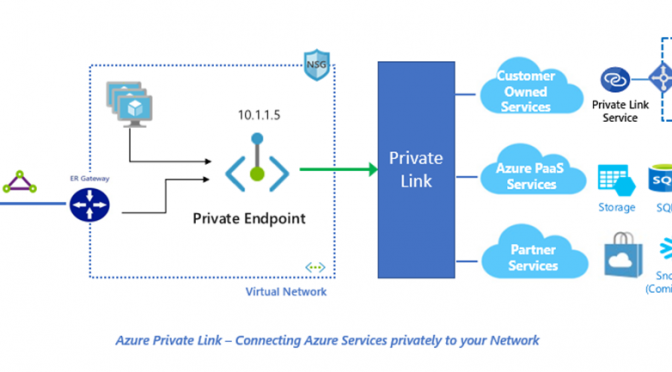
Azure allows to use IaaS and PaaS solution together over the same network. But all Azure PaaS services using a public interface for connection. When configure the PaaS firewall to allow traffic only from internal VNETs the public interface still exists. With Azure Private Link there is a new service to disable the public interface and add a private endpoint to secure connect to PaaS from your own VNET.

When configuring the internal service Firewall to block all traffic from outside the VNET, the Firewall make a mapping from internal VNET traffic to the Public IP and block all other IP- Adress ranges – and here comes the new Azure Service Private Link into play. This blog post will cover how Private Link works and how to configure this service for your environment including own DNS solution to get a complete private based Azure VNET.
Contents
General
Azure Private Link was announced during the MS Ignite 2019. Before the service available all Multi instance services in Azure only available via a public interface. The traffic flows from a internal source, like an Azure VM, to the Firewall. The Firewall then map the traffic via NAT to the public interface. This means without Private Link every multi instance service has it´s own Public IP and only an configured Firewall disable the possibility to reach the service from the Internet. Enabling Azure Private Link give the service an internal, private IP-Adress directly from the defined VNET IP-range, remove the public interface and secure your service .
Availability
Azure Private Link is in preview and available in all global regions. But not all Azure PaaS are supported with Private Link right now. The PaaS will be onboard step by step, take an eye on the list with all supported services until now.
Features
Azure Private Link support the following features:
- Private interface for Azure PaaS
- Support for On-Premise and peered Networks (VNET peering)
- Higher security because the PaaS has only a private endpoint
- Extending own service over private Link with Azure Loadbalancer
- Integrated with Azure Monitor
Difference between Private Endpoint and Service
There are two private link service available – Private Endpoint and Private Service.
Private Endpoint
A private endpoint means an private interface which is assigned to a PaaS inside your tenant and interacts over the assignend private IP.
Private Service
With the private service it is possible to make an own service available over private link as example when you are a service provider. In this scenario the service resides into your own VNET and will be accessible via a Load balancer for external customers.
How to create a private Endpoint
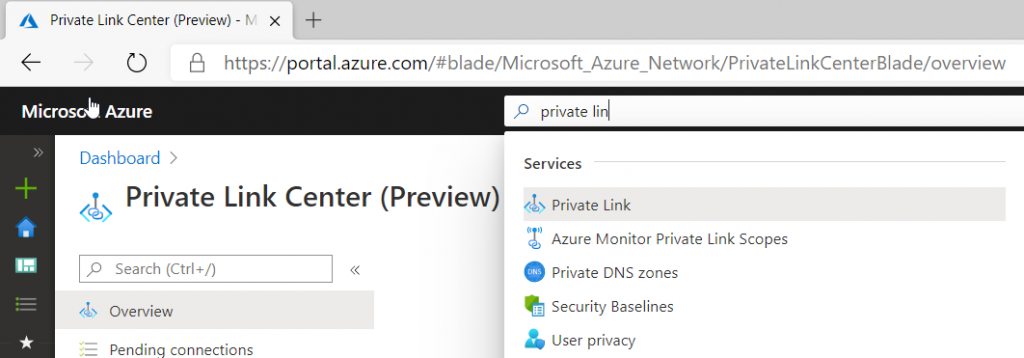
There are two ways to create a private endpoint for a PaaS – from the service side or from the central management side. This article discusses how to create it using the central private link management board. When using the portal, type “private link” in the search bar and use the icon to open the management page.
It is important to know that both resources PaaS and VNET must be located in the same region.
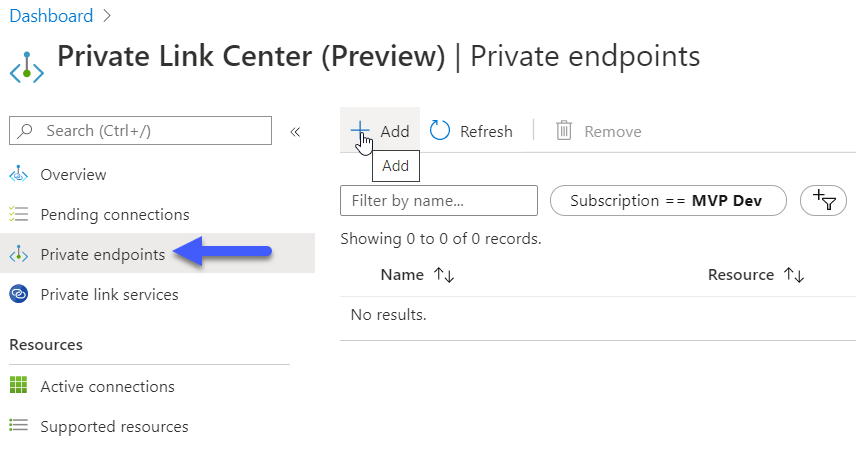
To create a private endpoint for an available PaaS going to “Private Endpoints” and select “Add”.
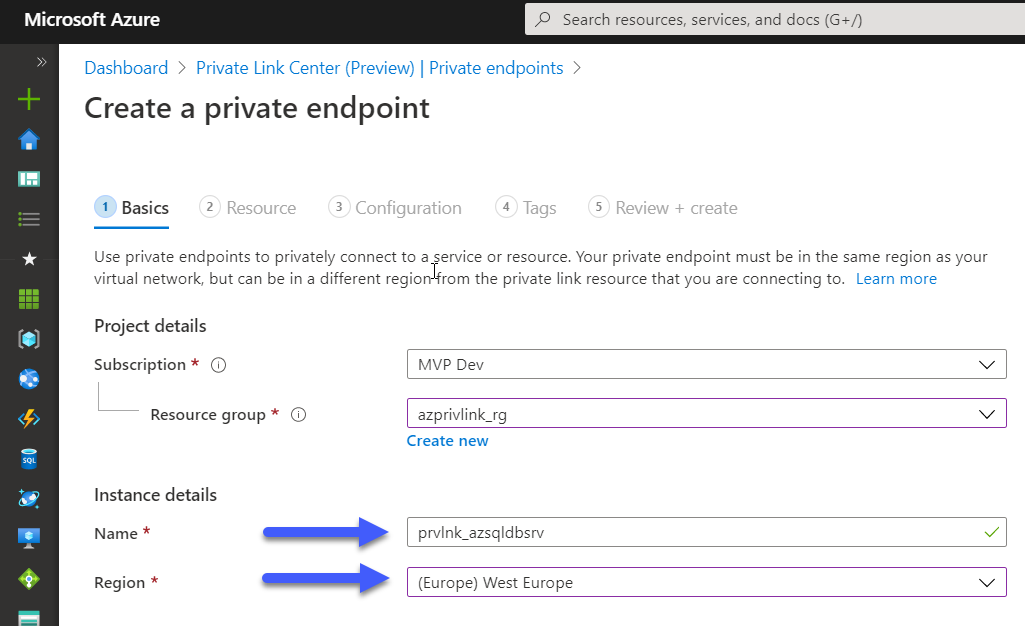
Enter the subscription and resource group details in the first blade. Create a Name for the private endpoint – please use a Namingconcept. In my environment I use the prefix “prvlnk” for all private link services followed by the name of the ressource. Choose the correct region, the private link and the region of the resource must match and click “Next”.
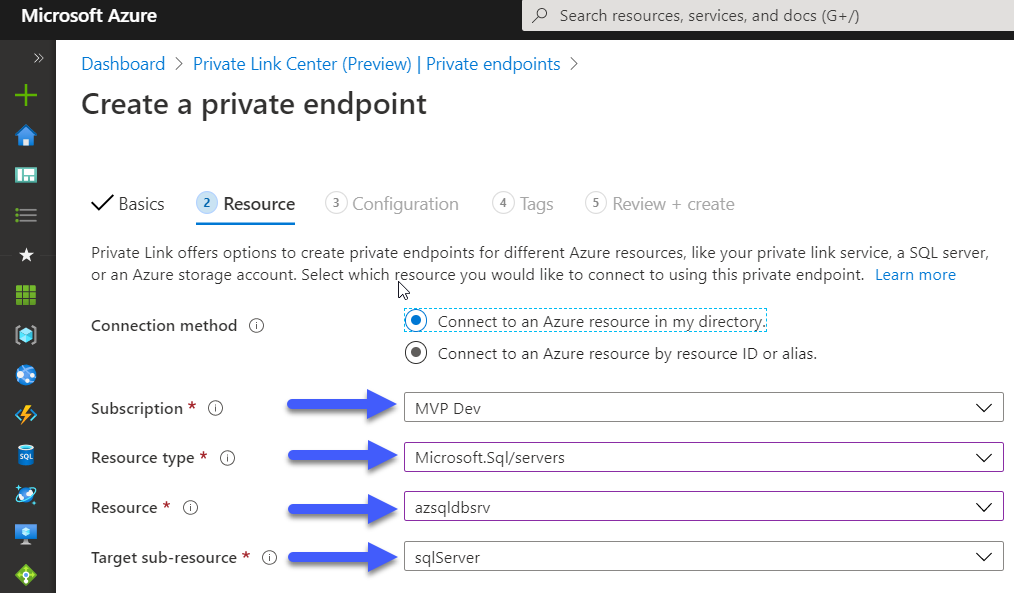
In the next window the resource information is requested. Enter the necessary information of the planned resource. Select the subscription, the resource type (keep in mind not all resources are supported right now – for example MySQL) and the resource. The information of Target sub-resource will be filled out automatically.
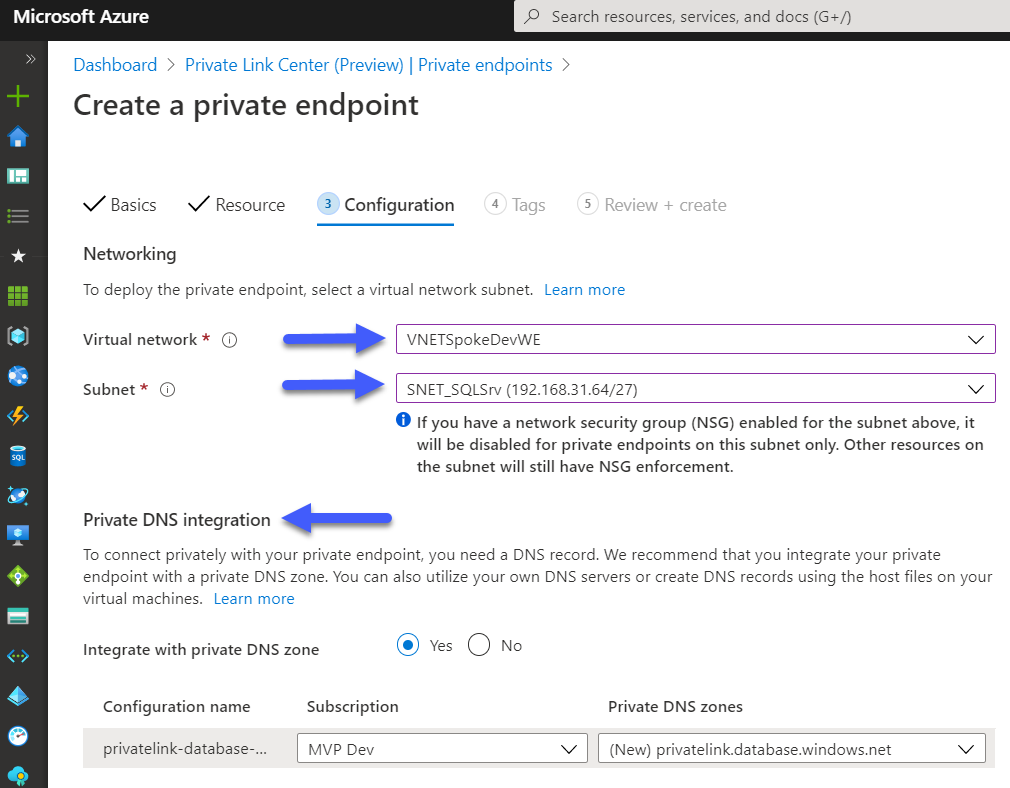
The resource blade is the intersting part for the private endpoint. Here will define in which VNET and Subnet the resource will get the private endpoint. Select the planned VNET and the subnet – the PaaS get the next free private IP from the selected VNET/subnet.
Private DNS integration
The private DNS integration give the possibility to enable DNS resolution for the PaaS private endpoint into a private DNS zone. This is a great way to manage private DNS zones without managing DNS server.
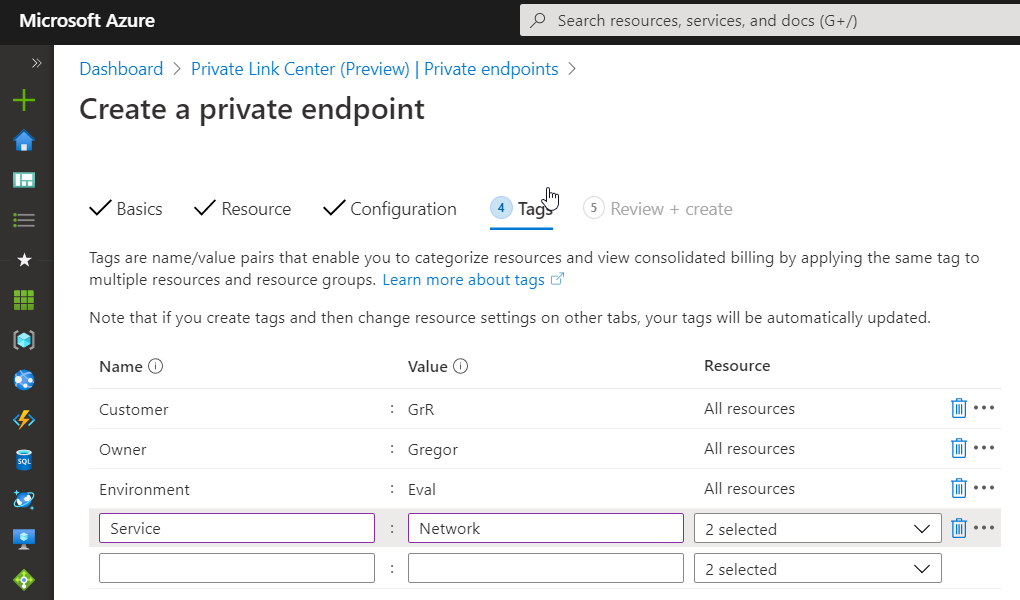
Add tags, review the selected configuration and finally Create the private endpoint.
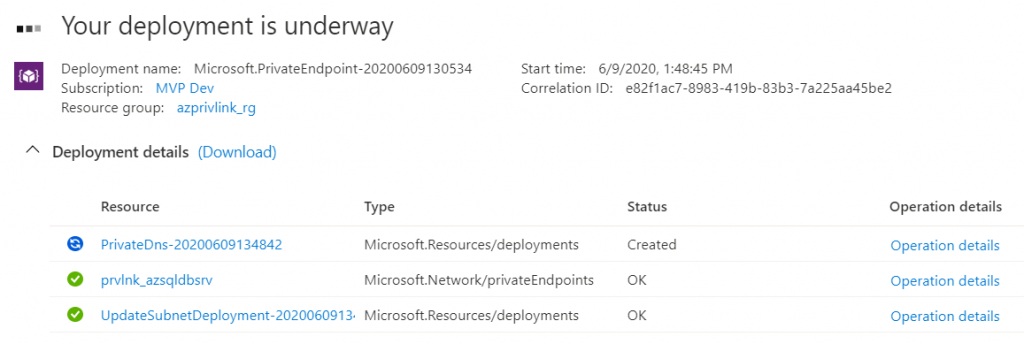
The Azure resource manager deployed the ressources and after finishing the new private endpoint is available in the Private Link center.
Secure your PaaS from public interface
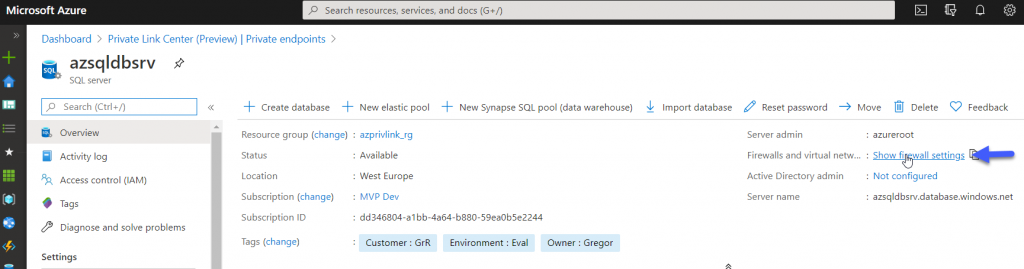
Now we had finished the creation of a private link for our PaaS, but the public endpoint still exist. To disable the public interface we can go over the Private Link center to the resource and select the firewall settings.
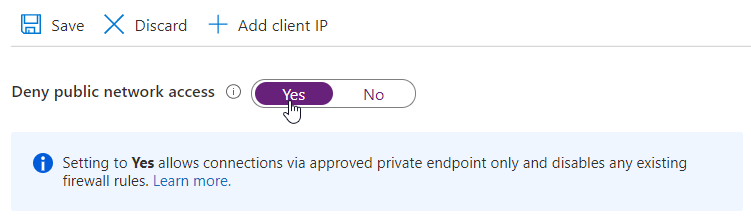
Before disabling the public interface, verify that related services can reach the PaaS through a private endpoint to avoid downtime.
Set “Deny public network access” to Yes and Save the setting. Now the PaaS is only available via the private endpoint.
Pricing and SLA
Azure Private Link has it´s own pricing modell and will be paid hourly based + incoming/outgoing traffic. The private link service is free of charge except for incoming and outgoind traffic.
| Private Link Service | free |
| Private Link Endpoint | 0,009€ per hour |
| Incoming traffic | 0,009€ per GB |
| Outgoing traffic | 0,009€ per GB |
| SLA | 99,99% |
thanks for sharing